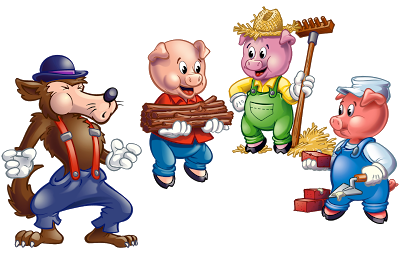
Once upon a time there was a company who had three computers within its infrastructure.
The first computer was placed on the DMZ and was configured by default by the IT Manager. Through a penetration test, several vulnerabilities arisen: the passwords were weakly crafted, more services than needed were published, the software was not configured properly, no access-lists were configured, and the system was outdated. Then, the Ackcent Analyst searched rainbow tables, performed active scans and used different exploits to take full control of the machine.
The second server was located on the Backend zone, publishes a service that was not intended to be used which was vulnerable to a zero-day exploit. Searching the Internet and developing a Proof-of-Concept of the found exploit, the Ackcent Security Analyst could compromise the information confidentiality.
The last computer was also on the DMZ, but it was hardened following Ackcent Cybersecurity guidelines and regularly tested by its Analysts. Surely that one day, any vulnerability could be discovered, but the maintenance and regular tests enhance the overall security at every finished cycle.
Our team suggest you protect by using a strong configuration, use the minimum number of required services, keep updated and constantly informed about new vulnerabilities.
If you have seen a similarity between that story and a popular tale, trust us. Ackcent Cybersecurity Analysts are here to support you and not to blow your house.
Have you ever been compromised by a security breach? What are the steps you take to keep yourself protected? Share your guidelines with us and feel free to contact us for further assistance.